Divided we stand.
-
My blog
I write mostly about security, mail, web and linux. My contacts are: mail://me@andreybondarenko.com and shaman007 all around Telegram, FB chat, WhatsApp. Primary use me@andreybondarenko.com and @shaman007:matrix.andreybondarenko.com Buy me a beer / Автору на пиво: shaman007@andreybondarenko.com (paypal)17QxrNyk9BCrP6LGUbqCNnXCzu4oeoYKaH (btc) 0x57500960FBC986225209E597D5B97065A9A10043 (eth) Links turned out to be useful / не потерявшие актуальности ссылки: Растаможка автомобиля из России в ЧехииПоиск работы…
-
Резервное копирование: как не плакать
Навеяно постом адвоката Сологуба, который я воспринял близко к сердцу: потеря архива документов для меня – страшный сон. А тут – чужие документы! DISCLAIMER: Я не буду долго расписывать теорию и почти не коснусь события “ОБЫСК“. Я буду считать, что хранимое не приводит к гибели людей или серьезным потерям юрлиц. Будем считать, что у вас…
-
Hardware upgrade
Now there are 4 OrangePI 5 there with NVME SSD storage and Ubiquity switch.
-
Yet another cluster update
UniFi: made a deployment and network setup. Does not see AP’s. 10001 UDP seems to be a problem, yet no idea why. Adopted them manually via SSH, now they work. Yes, consumes RAM for no reason. Why? No idea. However, the functionality is limited compared to the Windows app, and it does not provide me…
-
Cluster update
Out of all services, only Mastodon and UniFi Network controller are left, both are technically possible, but require strange things. Own Bitwarden service works great, however, needs a license to be OTP key. The Minecraft server works great. Done log aggregation, local Docker registry, metrics to have them in Lens, backups of everything. The phone…
-
OpenSource!
https://github.com/shaman007/Dockerfiles – Dockerfiles for my setup! https://github.com/shaman007/home-k3s – k8s (well, k3s) YAMLs I have to run everything.
-
This day
This day faster.cz closed 25/TCP/v4 to the outer worlds. What a shame!
-
OrangePi 5b emmc support
Armbian image from https://www.armbian.com/orangepi-5/ by default thinks that the board is 5, not 5b, so no nice emmc storage for you! I thought that it’s kind of general issue with the kernel, but all it took is to change fdtfile to rockchip/rk3588s-orangepi-5b.dtb in the /boot/armbianEnv.txt. Now my /var with all K3S and rancher stuff is…
-
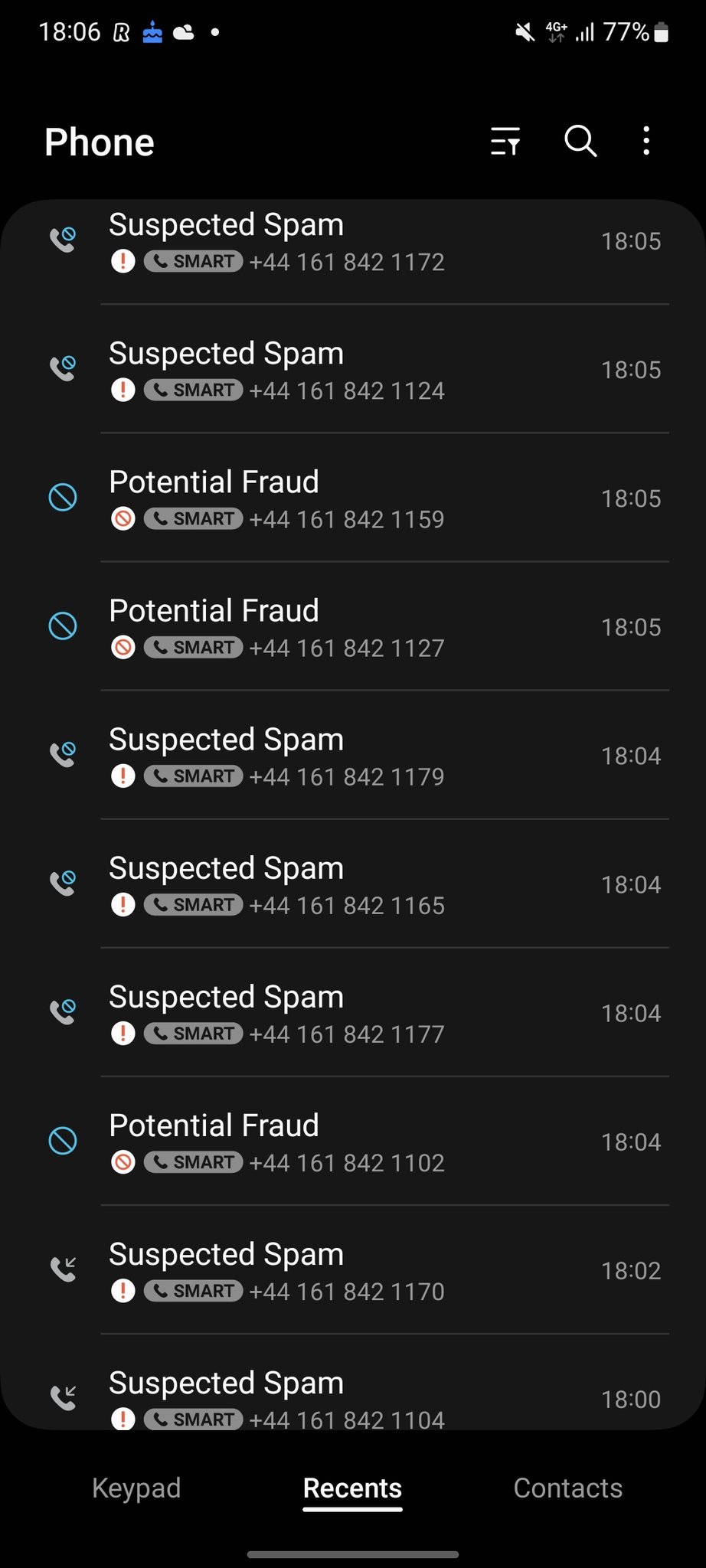
Another spamer went crying after a short dialog with me.
Got any book recommendations?